Group 1: "Team Sunny" (Sunny Kullar, Gilbert Comeau, Josh Vanderleest, Carlie Arsenault)
Contents
- 1 Group Notes
- 2 Group Introduction
- 3 Initial Statement
- 4 Defintion of an Online Predator
- 5 Technology and Issue
- 6 Types of Internet Predators
- 7 How They Select Their Victims
- 8 Who is at Risk?
- 9 What They Do With Their Victims
- 10 How They Utilize Technology to Attract Their Victims
- 11 Media Exposure
- 12 Social Programs Put in place to educate the public
- 13 Technology used to combat predators
- 14 Government and Police Initiatives to stop Predators
- 15 Interesting Information
- 16 References
Group Notes
Hey Just look at stuff thats been layed out as a skeleton and pick a topic post which topic your doing so were not doing the same and then do some research and add your info. I put some guiding questions under some of the topics feel free to add what you think is neccessary. Thanks Sunny Nov 22
Hey...I started working on our powerpoint. I'm about half way done it so when hopefully it will be done tomorrow and I will email it to all of you and you can tell me what you think and if anything needs to be added/deleted. Thanks, Carlie Nov 28
Group Introduction
Computer Science 203 Fall 2008
Tutorial 23 Group #1
Members of "Team Suny" - Suny Kullar, Gilbert Comeau, Josh Vanderleest, Carlie Arsenault
Initial Statement
The internet has developed into a worldwide phenomenon that many of us can’t live without, whether it is just aimlessly surfing the web or connecting with friends half way around the world. The internet has introduced many new things to the world. But for every positive of the internet, there is always a negative. With the introduction of chat rooms and social networking sites such as Facebook and Lavalife and so on, deviants known as internet predators have emerged. These people use chat rooms to find their prey, ranging from innocent teens to adults. Most of these predators target children in the age group of 12-15 who are searching for a companion. They lie about their age and pose as young teenagers, an age group which is attractive to these teenagers. The acts committed against these teens are some of the worst known to man. They range from rape, sexual exploitation including child pornography, human trafficking and, in extreme cases, murder. Our group will explore how these predators attract their prey, what they do with them, and what parents and students can do to protect themselves and their children against such acts.
Defintion of an Online Predator
An online predator is someone who uses the internet to exploit vulnerable people for sexual (or financial purposes. They:
- try to gradually seduce their targets through attention, affection, kindness, and even gifts
- are often devote considerable time, money, and energy to this effort
- are aware of the latest music and hobbies likely to interest kids
- listen to and sympathize with kids' problems
- try to ease young people's inhibitions by gradually introducing sexual content into their conversations or by showing them sexually explicit material [7]
Technology and Issue
Technology- Chat rooms and the world wide web
Issue-Explotation of children through chat rooms
Types of Internet Predators
The Two Minute Man
The "two minute man" is essentially what the name is. They are the type of predators children are warned about and are the most easily spotted. They begin with a slow stream of sexual questions to the child and, depending on the responses, will either continue or stop. The two minute man will try to determine if there is a possibility of contact and if there isn't or it seems to risky, they will quickly leave in search of someone easier. [5]
The Tactics User
This type of online predator has many varying styles but in essence, are mostly the same. They begin out with a stream of questions to determine if it is "safe enough" to talk to the child. They will ask such questions like "Are your parents home?" "Is the computer in the family room or in your room?". The next step the tactic user will take is to establish a quick bond with the child by asking questions about their lives. After these tactics are well established, the predator is free to steer the conversation anywhere he wants. [4]
The Big Brother
The "big brother" type is one similiar to the "groomer". He wants to come accross as the caring older brother. He engages in conversations with the minor, builing up trust. The conversations are shorter than the groomer conversations and sexuality is brought up much earlier. He is more sly that the two minute man but less subtle than the groomer. [5]
The Groomer
The "Groomer" is quite possibly the most dangerous type of online predator. They act as a parent type figure to the minors they are talking to. They are encouraging the teen to go outside, hang out with friends, to spend less time on the computer. The groomer will spent hours and weeks and months listening, giving advice, building trust with the one they are stalking. After there is a strong foundation of trust and emotions, the groomer will then bring up the subject of sexuality. [4] [5]
How They Select Their Victims
- internet predators favor children who have regular (and private) access to a computer
- internet predators gravitate towards children who are online for lengthy periods of time each day, and usually at the same time of day, predators seek children whose schedules mesh with their own, children who are online most days during a consistent time frame
- internet predators prefer children who have instant message accounts
- internet predators search out children who will speak to them, predators are forced to pass over children who refuse to communicate with strangers they have not met offline
- internet predators search out children who are vulnerable and lonely, sheltered and naive
- internet predators are all the more emboldened if they find out a child is from a single parent family, having trouble at school or with the law, or has been experimenting with drugs, alcohol or sexual activity.
- internet predators search out children who post personal profiles on the internet, especially those that provide name, age, photos, gender, physical description, telephone number, address, etc.
- internet predators favor targets who own webcams or digital cameras
- to be successful, internet predators require children who will not terminate the relationship at the first suggestion of sexual activity
- internet predators seem to favor victims between the ages of 12-15 [8]
Who is at Risk?
Young adolescents are the most vulnerable age group and are at high risk of being approached by online predators. It is at this age that most individuals begin exploring their sexuality, moving away from parental control, and looking for new relationships outside the family. Under the guise of anonymity, they are more likely to take risks online without fully understanding the possible risks and implications.
Young people who are most vulnerable to online predators tend to be:
• those new to online activity and unfamiliar with net etiquette
• aggressive computer users
• the type to try new, edgy activities in life
• those actively seeking attention or affection
• rebellious in nature
• isolated or lonely
• curious
• confused regarding sexual identity
• easily tricked by adults
• attracted by subcultures apart from their parents' world
• The child is viewing pornographic images on a regular basis.
• The child is receiving phone calls from strangers
• Mail, expensive item or packages arrive from an anonymous source
• The child spends an excessive amount of time on the internet at night.[5]
Kids feel they are aware of the dangers of predators, but in reality, they are quite naive about online relationships. In focus groups conducted by the Media Awareness Network, girls aged 11 to 14 initially said they disguised their identities in chat rooms. They admitted, however, that it was impossible to maintain a false identity for long and eventually revealed personal information when they felt they could "trust a person."
Building this "trust" took from as little as 15 minutes up to several weeks - not a long time at all for a skillful predator to wait.
What They Do With Their Victims
Indecent Exposure to Material Online
- predators tend to show their victims pictures of indecent material online via instant messages or chat rooms
- this can be part of the larger attempt to lure a child into having an illicit relationship
- they will attempt to use such images to convince a child to commit sexual acts, or to meet with them to engage in sexual activities [9]
Alicia Kozakiewicz's Story
Six years ago, Alicia Kozakiewicz says she was just a normal 13-year-old girl. That all changed on New Year's Day 2002. An online sexual predator befriended her in an Internet chat room, then kidnapped her, drove her across state lines and locked her in a cage in his basement, where he beat her, tortured her and raped her. "The boogey man is real. And he lives on the Net. He lived in my computer -- and he lives in yours. While you are sitting here, he is at home with your children." Her parents were told that there was a one in a million chance that she would be recovered. But, by a stroke of luck, the FBI had found her. She says that although she was rescued, "Make no mistake -- that child was murdered. I know now that some parts of me are forever there. The child that I was is still chained in that room, still suffering." [11]
Her testimony of her experience and against sex predators online can be found at: http://www.brightcove.tv/title.jsp?title=1255395849
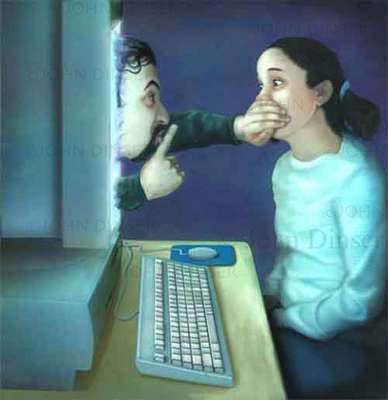
How They Utilize Technology to Attract Their Victims
Internet
Before there was internet, a predator would have to go out into the real world and find kids the old fashioned way. They would have a big risk of revealing themselves if they had tried to harm a child in the public's view. But now, with the internet, things have been made a lot easier for the predators. The internet has provided an unique communication forum that is allowing predators to connect with as many children as they could possibly want without having to meet face to face. [9]
Cameras
Digital cameras are now also a great aid for online predators. Before digital cameras were invented, predators had to invest in equipment to develop their pictures or find someone willing to do it for them. Now, predators are free to take as many pictures as they want to and upload onto their computer in a matter of minutes. The pictures are also free to be easily spread around the internet. They can be emailed to anyone in just a few seconds or posted on a web page for anyone to view. [9]
Webcams
Webcams are also a new technology used by many online predators. The webcams can be used as a video camera basically and can be viewed live by many other people on their computers. It is a quick and easy way for one predator to share findings with others.[9] The webcam can be used to expose children to indecent material or even get the child to perform an assortment of actions on the webcam for the predator's viewing.
Language
Many online predators use abbreviations and codes in instant messages. Even if a parent reads the instant messages, most will not be able to understand what the conversation is about. The most famous ones are: [10]
A/S/L - age/sex/location
LMIRL - lets meet in real life
A detailed list of many acronyms is available at http://www.wikihow.com/Understand-Chat-Acronyms
Media Exposure
Internet predation has become somewhat of a cultural and societal phenomenon as late, and it has slowly shifted further into the public eye. One of the main reasons for this is the increasingly popular NBC program "To Catch a Predator." 'Predator' is a reality television program in which older men are lured via internet chat rooms and 'decoys' (professionals who pose as young teens in chat rooms). The decoys converse with the men with the goal of arranging a meeting with them for the purpose of sex. The meeting is usually located at a house, but other locations have included a beach and various fast food restaurants. The would-be predators are lured by a young-looking decoy into the house, where they engage in a short conversation before the decoy makes an excuse to leave momentarily. At this point Chris Hansen, the show's host, emerges from another room and confronts the predator, usually with an ironic one-liner. He follows up with numerous questions about the predator's motivation and reason for visiting the house that day, allowing them to lie for a few minutes before producing the transcripts of the chats between the predator and the decoy. After a few minutes of additional questioning, he informs the men that he and his crew are doing a series on "adults who lure children for sex" on Dateline NBC and tells them they are "free to go", at which point they exit the house and are promptly arrested by police and taken away. [1]
Many people have lauded the series for bringing awareness of internet predation to parents across the country. However, it has also had its fair share of detractors. Many have vindicated the show (and Chris Hansen) for humiliating the men in the name of ratings. They argue that 'Predator' "lowers the standards, if that's possible, of our already revolting and brainless TV media to a new low," through the use of "voyeuristic drama." [8]
It has also had its share of debacles. In one such incident, the "To Catch a Predator" team thought it had caught a district attorney, someone whose documented capture would surely boost ratings and ensure greater viewership across the nation. However, when repeated attempts to lure the man to the house failed, the crew decided to confront the man at his house, where, upon seeing the police, the man committed suicide via gunshot to the head. [5]
Social Programs Put in place to educate the public
The message for parents: Be watchful of your kids' online activities.
The message for predators: Exploiting a child online is a federal crime and could have lifelong consequences.
These are the key issues being spread by the governments of many nations in an effort to raise awareness about the growing problem of online predators. The media is broadcasting PSA’s, focusing both on potential targets and their parents, and the predators themselves. These are meant to warm minors about the very real threats of being careless while online, and to get through that this is a very serious federal offence to those who are taking advantage of the net naïve.
There are many websites that have been constructed with the exact purpose of raising the public awareness of this subject. One such site is http://predator-awareness.healthylifestylegeek.com/, which lists many ways in which to identify a predator, and what to do to avoid getting drawn into their games. Some are government sponsored, and others are privately run, but all of them tell basically the same tips and advice to any Internet user. Be careful.
Technology used to combat predators
Net Nanny
Technology used to catch predadors: "Net Nannny" is a somwhat new program that lets parents take the fight up against predador's themselves. The Program is installed into a computer and then it is able to monitor and stop actions that parents would rather thier children not take part of.The Many features of "Net Nanny" include:
Prevent your Address, Phone and Credit Card numbers from being given out on the Internet. Net Nanny provides users with FREE "Can Go" and "Can't Go" site lists to download into their Net Nanny screening databases. The lists are updated regularly so visit anytime. NO monthly site list subscriptions! Prevent other personal or sensitive data from being given out on the Internet. Prevent loading, downloading and running of unauthorized software or CD-ROMs. Prevent User definable 'Words', 'Phrases', sites, URLs, News Groups and IRC Chat Rooms from being sent from, received by, or accessed by your PC. Mask inappropriate words, phrases or language. Block images too! Screen individual sites you know the name of like "Playmate.html". Or block all GIFs or JPGs and release the function when you're supervising. Prevent your disks and hard drives from being reformatted. Prevent your files from being deleted or tampered with. Develop your own screening list for'Sites', 'Words', 'Phrases' and subjects. Complete Audit Trail of monitored 'sites', 'Words', 'Phrases' and user-defined content on the PC. Audit Trail indicates PC start-up, and triggered violation shutdown item dates and times. Operates with all major Online Providers and in e-mail and IRC. Extra security provided through multi-user passwords and properties. Net Nanny has other convenient functions. All you have to do is tell Net Nanny what you do not want entered or received on your PC terminal. Select the terminal action you want to take for violations: Monitor, Log, Mask, Warn, Block, Application Shutdown, or all. Administration Program allows access to all Net Nanny functions. Leaves no extra files on disk when removed. Cannot be turned off unless done through the Administration Program. Net Nanny operates with or without users knowing.[1]
WickedTravelAdventures
The FBI has also taken initaitive in the fight agaisnt internet predadors by creating a bait or fake website. This website called "WickedTravelAdventures" and targets predadors heading to Thialand and Indoniesia. There are sevaral options and material on the site that include: In their news group postings, agents with the FBI's Maryland-based Innocent Images Task Force wrote that the firm catered to clients "who want to travel to Exotic destinations accompanied by your specified companion," adding that "we provide you with confidentiality and safety as a top priority." The Wicked Adventures site uses meta tags in its html pages to presumably lure prospective clients. Terms embedded in the site's pages include "sex tourism," "lolita," "nymphet," "asian virgins," "pedoland," and various phrases associated with child pornography ("pthc," "hussyfan," and "babyj"). Additionally, a "confidential information form" on the site asks prospective travelers about "age preference" for their "companion." The choices are 12 and under, 13-15, 16-17, and 18 and above. The form also seeks information about preferred activities and special interests. A screen grab of the Wicked Adventures homepage can be found below. The FBI operation led yesterday to the arrest of Gary Evans, a 58-year-old Florida man who allegedly sent an August 2005 e-mail to the Wicked Adventures site proposing a partnership. Evans, pictured above, offered to help the company expand its sex tours to Honduras and Costa Rica, according a criminal complaint filed in U.S. District Court in Orlando. Charged with arranging illicit sexual conduct with a minor, Evans faces a maximum of 30 years in prison if convicted of the felony count. [2]
The FBi aslo posts fake links on the internet, that allow people to downlaod "child pornography". Instead of real pornography the individual recieves a program that sends the users IP adress to FBI officials. The predador is then tracked down arressed and charged.
Web Watcher
Web Watcher is a computer monitoring software that can be used by parents to know exactly what their children are doing online and therefore can take the neccessary measures to protect them. [6] It allows you to:
- read every email that is sent and recieved
- see every instant message/chat they participate in (both sides of the coversation)
- see every webpage they visit and how long they stay there
- block access to inappropriate websites
- capture every single keystoke they type (including usernames and passwords)
- limit access to what software programs can be used
- take screenshots of their computer screen
- monitor and control laptops no matter where they go
- monitor as many computers as you need to
- be notified when "alert words" you choose are used in any communications
Government and Police Initiatives to stop Predators
Police Involvement
Canadian police agencies, specifically the Onatrio Provincial Police (OPP) have taken the lead in the fight against Predators and have set the standard for North American police and government involvement."In June 2004, the government announced an extra $1 million in annual funding for the OPP's Project P. The additional funding allows the Child Pornography section to increase its number of detectives and acquire technology and specialized training."[4]
In the United States the FBI has devoted a whole unit called IINI towards the capture of Internet Predators and the safety of children using the web:
"The IINI is managed by the Innocent Images Unit within the FBI’s Cyber Division at FBI Headquarters in Washington, DC. Innocent Images field supervisors and investigative personnel work closely with the Innocent Images Unit regarding all IINI investigative, administrative, policy, and training matters. The IINI provides a coordinated FBI response to this nationwide crime problem by collating and analyzing information obtained from all available sources.
FBI’s Innocent Images National Initiative focuses on:
-Online organizations, enterprises, and communities that exploit children for profit or personal gain.
-Major distributors of child pornography, such as those who appear to have transmitted a large volume of child pornography via an online computer on several occasions to several other people.
-Producers of child pornography.
-Individuals who travel, or indicate a willingness to travel, for the purpose of engaging in sexual activity with a minor.
-Possessors of child pornography."[6]
Goverment Involvement
The Protect Our Children Act--which includes provisions introduced by Sens. Joe Biden (D-Del.), Hillary Clinton (D-N.Y.), and John McCain, (R-Ariz.)--sets requirements for Internet companies to report incidences of child pornography. It also authorizes more than $320 million for the Justice Department over the next five years for, among other things, the Internet Crimes Against Children Task Force.[8]
The KIDS Act introduced in 2008 requires sexual offenders to register their email addresses and other online identifiers that they use. The American Department of Justice will house this information in a secure database and permit certified social networking sites to securely contrast their subscriber lists against the sex offender database. [9][10]
Acts like these have been introduced in America to keep tabs on known internet predators. This legislation is targetted towards social networking sites and ensures that these sites can compare user information to a database of known offenders and notify authorities if their is problem.
Interesting Information
Center for Exploited Children - Internet Predators Commercial
http://www.youtube.com/watch?v=GrG0qJQXaTc&feature=related
The Story of Emily - a video based on a true story of an internet predator and a teenager's relationship as it grows from conversations on the internet to sharing pictures to meeting face to face.
http://www.youtube.com/watch?v=_cG3igRo_Rc&feature=related
Internet Predators Using Secret Code - A news report on the slang and abbreviations that online predators use
http://www.youtube.com/watch?v=iGTmcspxUc8
References
Sunny Kullar
1.http://www.stopinternetpredators.org/news/
2.http://www.stopchildpredators.org/legislation/
4.http://ogov.newswire.ca/ontario/GPOE/2005/01/21/c5375.html?lmatch=&lang=_e.html.
5.http://www.pathoy.onmpp.ca/TacklingInternetPredatorsChildPornographers.htm
6.http://www.fbi.gov/publications/innocent.htm
7.http://www.nap.edu/netsafekids/pp_li_il.html
8.http://news.cnet.com/8301-13578_3-10064738-38.html
9.http://news.zdnet.com/2100-9588_22-151062.html?tag=mncol;txt
10.http://cybertelecom.blogspot.com/2008/11/keeping-internet-devoid-of-sexual.html
Gilbert Comeau
1. http://www.security-online.com/mall/vendors/netnanny/netnannyinfo.html
2. http://www.thesmokinggun.com/archive/0511061web1.html?link=rssfeed
4. http://www.govtech.com/gt/423132?topic=117671
5. http://peacesecurity.suite101.com/article.cfm/internet_threats_to_Children
6. http://www.wiredsafety.org/internet_predators/index.html
7. http://www.trutv.com/library/crime/criminal_mind/sexual_assault/internet_predators/1_index.html
8. http://en.wikipedia.org/wiki/Online_predator
9. http://da.lacounty.gov/pok/pokpredators.htm
Josh Vanderleest
1. http://www.bewebaware.ca/english/OnlinePredators.aspx
2. http://www.microsoft.com/protect/family/guidelines/predators.mspx
3. http://blogs.thenewstribune.com/crime/2008/11/14/title_712
4. http://www.stopanonlinepredator.org/media/
5 .http://www.KnowWhereTheyGo.org
6. http://www.awarenessistheanswer.com/modules/content/index.php?id=21
7. http://predator-awareness.healthylifestylegeek.com/
Carlie Arsenault
1. http://www.youtube.com/watch?v=GrG0qJQXaTc&feature=related
2. http://www.youtube.com/watch?v=_cG3igRo_Rc&feature=related
3. http://www.youtube.com/watch?v=iGTmcspxUc8
4. http://www.associatedcontent.com/article/173738/internet_predator_styles.html?page=1&cat=17
5. http://www.associatedcontent.com/article/173738/internet_predator_styles.html?page=2&cat=17
7. http://en.wikipedia.org/wiki/Online_predator
8. http://www.safer-internet.net/how-internet-predators-select-their-victims.html
9. http://www.senate.state.ny.us/sws/childsafety/rpt_internet.pdf
10. http://www.wikihow.com/Understand-Chat-Acronyms